Decoding function arguments
Today I will show you a feature that is pretty useful when analysing an application. We call it the “arguments decoder”, and it displays the content of a function’s arguments when its prototype is known. The latter’s definition can be either extracted from the msdn function and structures, or given by the user.
Here is an example:
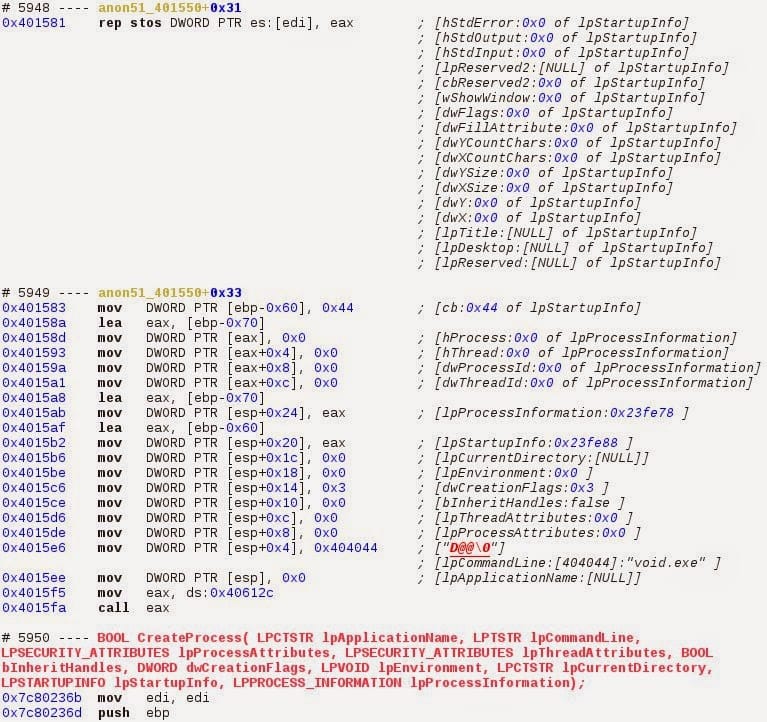
We see a call of the Windows CreateProcess() <http://msdn.microsoft.com/en-us/library/windows/desktop/ms682425%28v=vs.85%29.aspx>_ function. As you can see all the arguments are displayed along with their values as they are pushed onto the stack. If one argument is a structure, its fields will be shown as well. Here for instance the LPSTARTUPINFO structure:
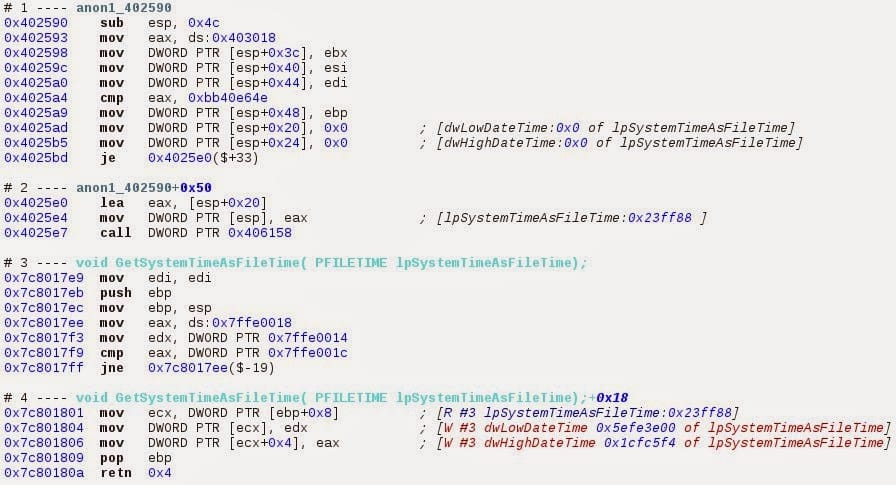
And since we can track all memory accesses with the Memory Range History inspector (cf this article, we know where and when the program reads or writes the arguments. Here we can see it for the structure FILETIME lpSystemTimeAsFile. The structure is initialized at sequence #1, the pointer is pushed on the stack at sequence #2. The structure pointer is read at sequence #4, and the structure fields are also written at the sequence #4.
It is still a work in progress feature but the new 2015-v1 version already ships with a very useful implementation.

